The Valiant Defense Series is a solitaire game system that allows players to play as the defenders of famous siege attacks throughout history. The series to date includes Pavlov’s House, which takes a look at the heroic Soviet defense of a fortified apartment building during the Battle of Stalingrad in World War II and Castle Itter, which focuses on a battle near the end of World War II where a motley assortment of US tankers and infantrymen, Wehrmacht officers and enlisted men, an SS officer, French prisoners and an Austrian resistance fighter defend a castle from an assault of SS, and have really enjoyed both.

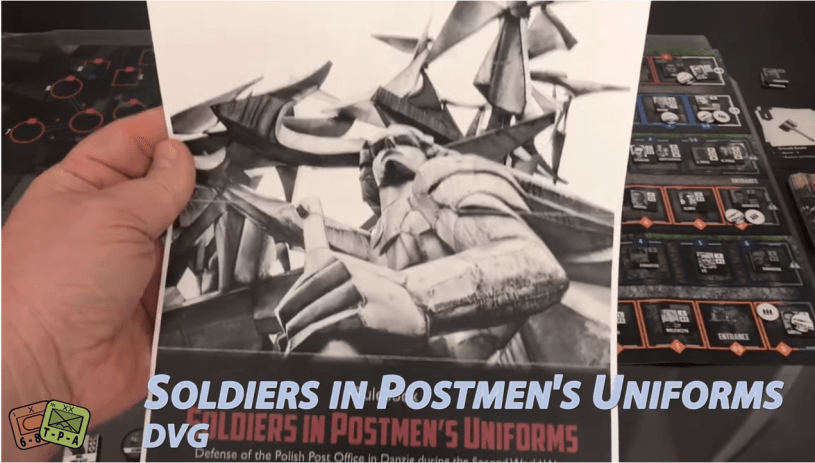
Now comes the third volume in the series called Soldiers in Postmen’s Uniforms which deals with the assault on Polish Postal Office #1 in the Free City of Danzig, Poland on the first day of World War II. This game tells the story of the assault as German forces moved in to seize Polish installations. Two of the installations were on alert and under orders to hold out: the Military Transit Depot on the peninsula of Westerplatte and the Polish Postal Office No. 1. The personnel of the post office repulsed repeated assaults, and were forced to surrender only after a day-long siege, when the post office was doused with gasoline and set alight. Though German propaganda cast these acts of defiance as futile and a failure, they were viewed by the Polish people as symbolic of their stand against a materially superior aggressor.
The game comes to Kickstarter today (November 17th) and I played a prototype copy of the game and shot this 48 minute video with a simple explanation of the game play and my thoughts on the design. You can view that video at the following link:
We also published an interview with the designer David Thompson on the blog last week and you can read that at the following link: https://theplayersaid.com/2020/11/09/interview-with-david-thompson-designer-of-soldiers-in-postmens-uniforms-from-dan-verssen-games-coming-to-kickstarter-november-17th/
Finally, here is a look at an AAR of sorts from David Thompson as he played through the game on Tabletop Simulator that we posted on the blog about a month or so ago: https://theplayersaid.com/2020/10/13/playthrough-aar-for-soldiers-in-postmens-uniforms-from-dan-verssen-games-coming-to-kickstarter-soon/
If you are interested in the Kickstarter, you can visit the page at the following link: https://www.kickstarter.com/projects/danverssengames/dvg-soldiers-in-postmens-uniforms?fbclid=IwAR2hVPzSbXpLwUnaaVV6Oo9O9596G7lYeEibtUczwrqUh9e5T5OxExg0t6A
-Grant